It’s automatic, wireless, and oh-so-convenient.
Even before smartphones and internet-connected devices, Bluetooth was helping users exchange files with other gadgets without cables, cords, and other intermediaries. It’s still as effective today when modern technology has rendered radio waves obsolete.
Bluetooth allows people to make hands-free phone calls while driving. It also keeps their office desk tidy and cable-free by pairing their computer with the keyboard, mouse, and printer. While jogging, people use it to listen to music on their headphones and track their miles with a smartwatch.
But how secure the Bluetooth connection really is?
In the age of limitless connectivity, flexible boundaries have become a big security issue. You can use a VPN to encrypt your data and protect your smartphone, computer, and other internet-connected devices, but there’s no similar solution for Bluetooth.
Here’s what risks people face when they leave Bluetooth turned on, and how to avoid them.
Common Threats to Your Bluetooth Device
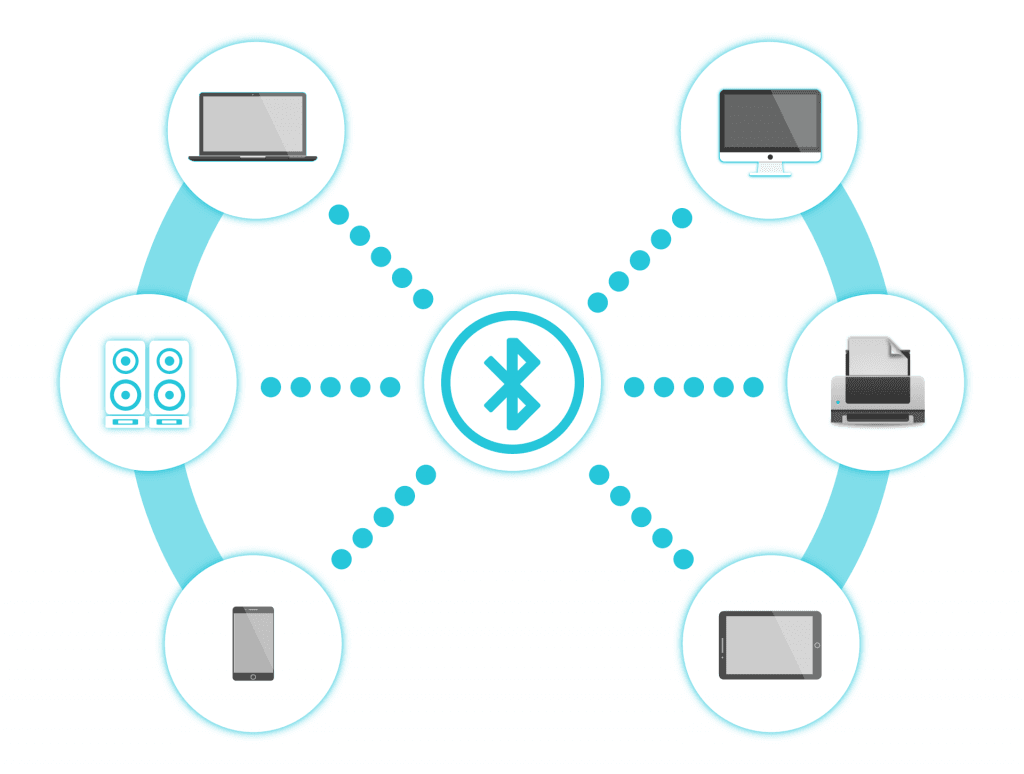
When you turn on Bluetooth to pair your gadgets or connect your device with somebody else’s, you get a list of available Bluetooth users that are nearby.. This is because Bluetooth works like an antenna – it picks up all radio signals in a certain radius.
But if you can see other Bluetooth-enabled devices around you, then so are your neighbors. Typically, you wouldn’t use this solution to connect to an unfamiliar device owned by a person you don’t know. The problem is, some shady people would.
The main disadvantage of Bluetooth is that it can be easily intercepted.
Criminals can use this weakness to steal the information you share via Bluetooth or to send you the information you didn’t ask for. Best case scenario, you might receive a file you don’t need and want. Worst case scenario, your device might get accessed and infected.
Here’s a list of attacks people might fall victim to:
- Bluejacking
Bluejacking is not so dangerous as it is annoying.
This type of attack entails unsolicited text messages, mostly advertisements that people usually don’t want to see. With Bluejacking, leaving your Bluetooth on exposes you to aggressive (and very ineffective) marketing tactics, but it doesn’t pose a threat to the device itself.
- Bluesnarfing
Unlike bluejacking, bluesnarfing is an actual threat to your security.
Using this method, criminals can break into people’s devices and gain unauthorized access to their data. They can see the text messages, steal contacts, and most alarmingly, get their hands on people’s passwords. Successful bluesnarfing results data and identity theft.
- Bluebugging
Bluebugging and bluesnarfing usually go hand in hand.
When criminals gain access to a person’s’ contacts, they can use them to send text messages and place calls from the phone without the user being aware of it. That way, they can spread bugs and viruses to a lot of people at once and break into hundreds of other devices.
- BlueBorne
But still, BlueBorne beats them all.
Unlike bluejacking, bluesnarfing, and bluebugging, which are usually restricted to phones, BlueBorne can take advantage of any Bluetooth device. If the detected device has any vulnerabilities, criminals can find their way in and wreak chaos.
More precisely, they can take control of the device, infect it with malware, or steal data. But it’s even more unnerving that BlueBorn can affect all vulnerable Bluetooth devices within an area without anyone ever noticing that something’s wrong.
How Can You Protect Your Bluetooth Device?
Not using Bluetooth at all would be an obvious solution, but this technology has too many benefits that are worth the risk. And since you can’t eliminate the risk altogether, the following security measures are the next best thing:
- Turn Bluetooth Off When You’re Not Using It
It’s pretty logical – whenever you’re not using Bluetooth, make sure that it’s turned off. Switch to a USB keyboard and mouse, since their Bluetooth variants must be turned on for hours while you’re working and can endanger your entire business team.
- Keep Your Bluetooth Up-To-Date
If you like your Bluetooth functionalities too much to keep them turned off, then you should at least use the latest versions of this technology. Just like with your computer, smartphone, and other devices, keep it updated at all times.
- Set Up Trusted Devices
Have a list of trusted devices on your Bluetooth-enabled computer, phone, and other gadgets. That way, you’ll have the option to accept or decline all unfamiliar devices that request to send you information using this connection.
- Make Your Bluetooth Non-Discoverable
Some Bluetooth-enabled devices come with a non-discoverable mode. If your favorite gadgets offer this option too, by all means, use it. This mode isn’t always effective against Bluetooth scanners and sniffers, but it does add some layer of security.
Until tech scientists come up with a better defense solution for our Bluetooth-enabled device, this is more or less everything we can do to keep it protected DIY-style. The good news is, they are working on it. Sooner or later, we’ll be able to enjoy its benefits in peace.